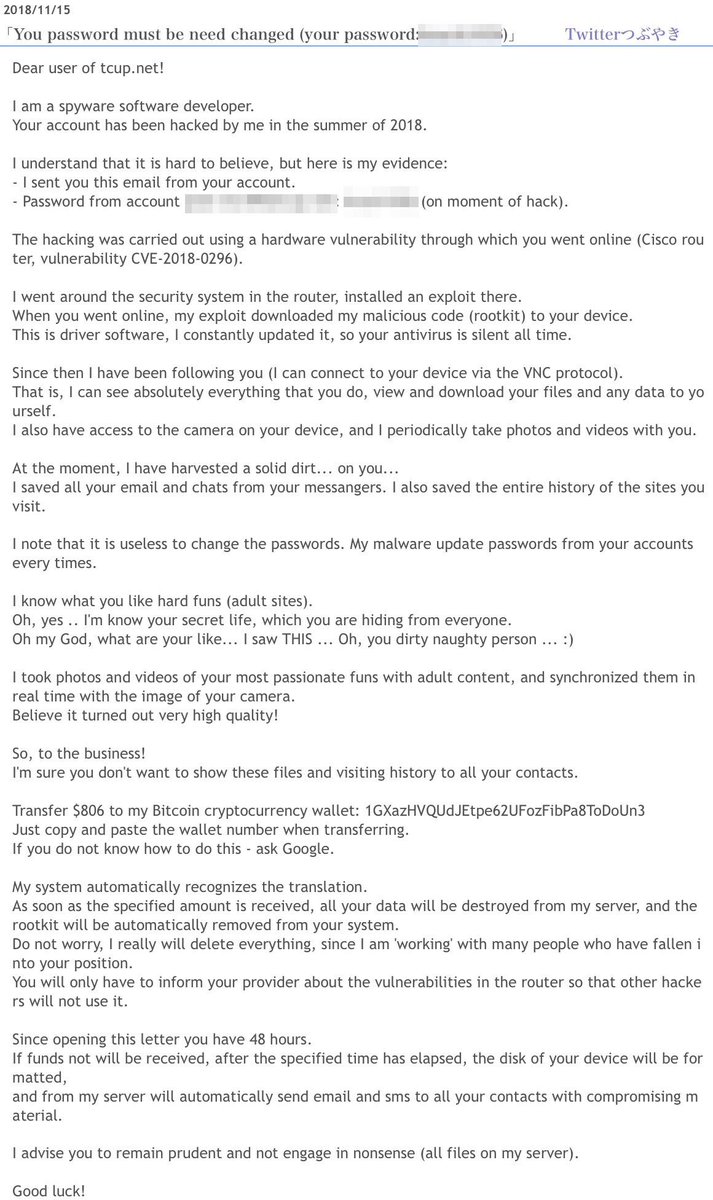
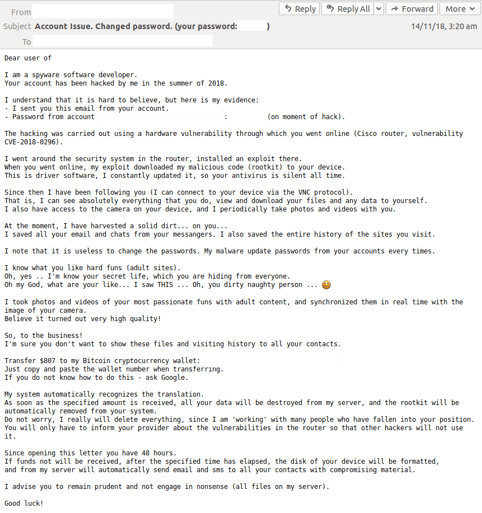
ねこさん⚡(ΦωΦ) on Twitter: "@jakecreps @Capteur_Ouvert @tbc0 @doseofgose @BenDoBrown @EFF #sextortion scam arrived at 11/22/2018 in Japan. Subject:<mailaddress> - this account has been hacked! Change your password <password> right now! BTC ...

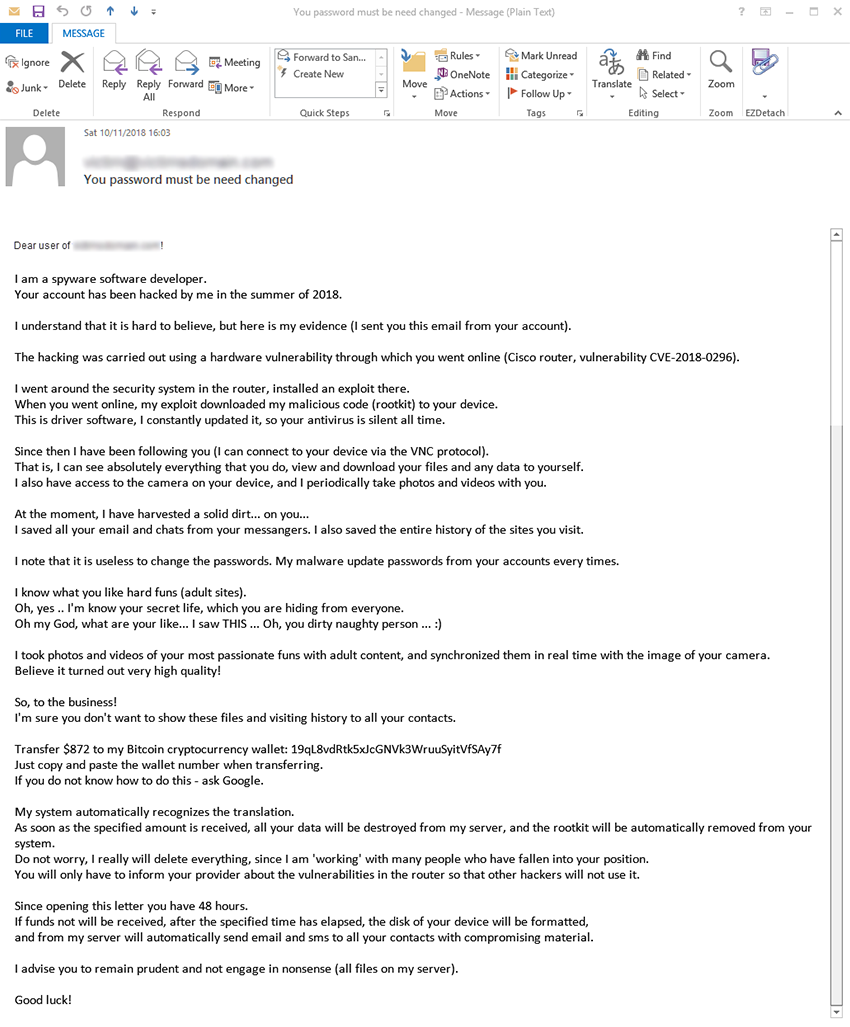
Phumzile Van Damme on Twitter: "The email scammers are trying hard shame. Unshaken. No bitcoin transfer coming from me. https://t.co/ANTymmaHTf" / Twitter

台中2B 月台:臉書候車處- 今天收到一封有趣的垃圾郵件,宣稱我的裝置被破解,連帶取得我的Google密碼,還特別用我的Gmail帳號寄信給我。並表示我的一切都在他的掌握之中。 (宣稱是透過「Cisco router, vulnerability CVE-2018-0296」這個漏洞) 最有趣的是,他提到的 ...
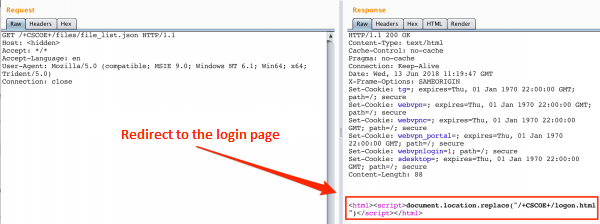
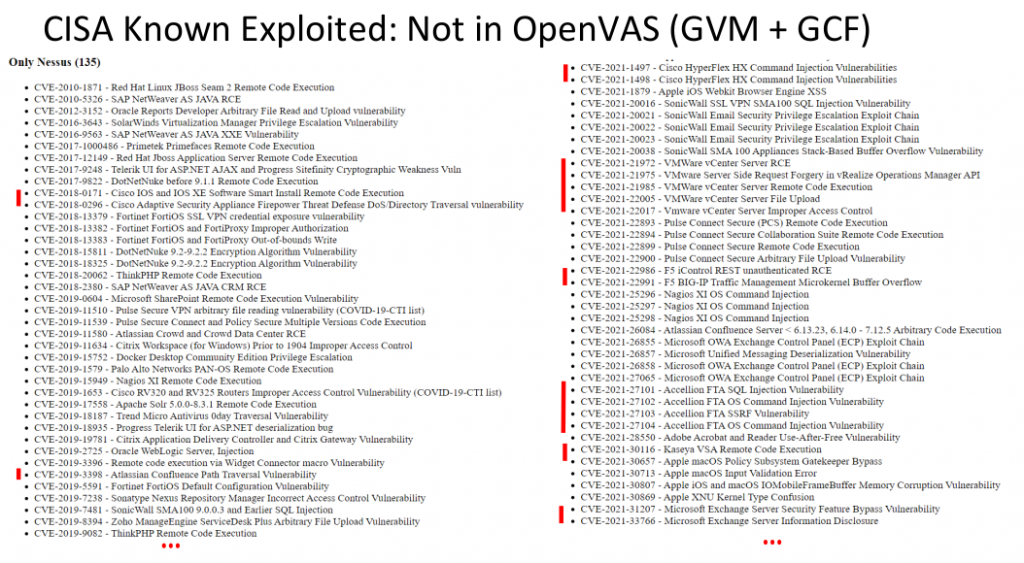
Description of CVE-2018-0296 vulnerability – bypassing authorization in Cisco ASA web interface. - research.securitum.com
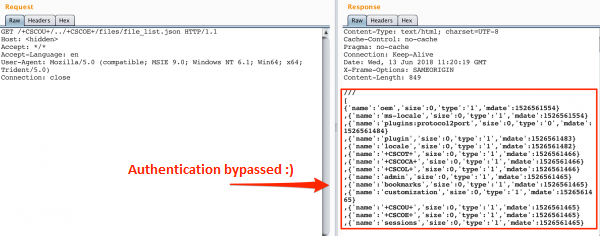
Description of CVE-2018-0296 vulnerability – bypassing authorization in Cisco ASA web interface. - research.securitum.com
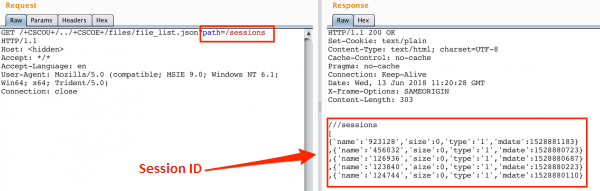
Description of CVE-2018-0296 vulnerability – bypassing authorization in Cisco ASA web interface. - research.securitum.com

Cisco PSIRT Notice About Public Exploitation of the Cisco ASA Web Services Denial of Service Vulnerability - Cisco Blogs
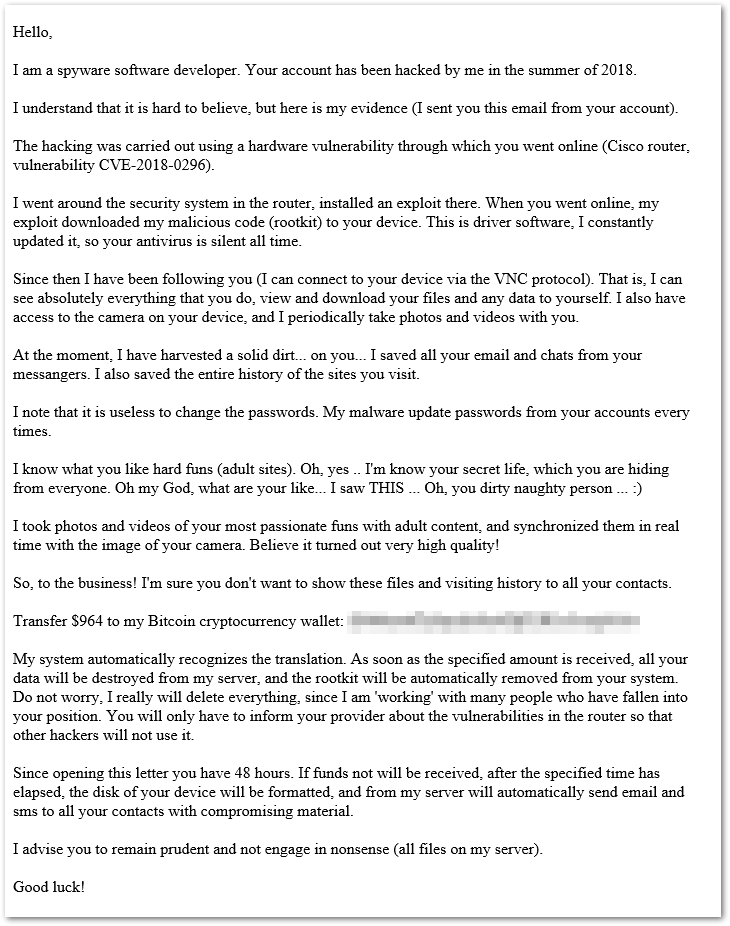
Have you received an email that demands ransom and claims to know your passwords? | ATUS | Western Washington University